This Article Explanation about cryptocurrency scam where The bull market euphoria of recent years has quietly evaporated, leaving behind a highly sophisticated, hyper-financialized Web3 ecosystem. The predators hunting in this space have aggressively adapted to the new terrain. Retail investors are no longer falling for poorly spelled emails from fake foreign princes or crude Twitter bot replies promising to magically double their Ethereum. The entire game has fundamentally changed.
Today, malicious actors operate with the chilling precision of nation-state intelligence agencies. They heavily leverage generative AI, exploit novel token standards, and manipulate decentralized finance (DeFi) primitives before developers even realize a vulnerability exists. If you genuinely want to survive the current market cycle, understanding the mechanics of these next-generation threats is not just recommended—it is absolutely mandatory.
The threat vectors of 2026 are completely invisible to the untrained eye. They do not look like scams. Instead, they look exactly like legitimate, highly audited decentralized applications backed by top-tier venture capital. Below, we meticulously dismantle the architecture of these modern frauds, exposing the technical nuances and psychological warfare driving the latest wave of cryptocurrency scams.
The Architecture of Modern Deception: Why 2026 is Different
Fraud in the blockchain space used to rely heavily on simple human error. A user would foolishly hand over their seed phrase, or a victim would manually send Bitcoin to a random wallet address. That era is definitively over. The current wave of sophisticated exploits directly targets the execution environment itself.
Scammers now actively weaponize the very tools originally designed to make Web3 user-friendly. Account Abstraction (EIP-4337), which brilliantly allows wallets to operate as programmable smart contracts, has tragically become a massive attack surface. Bad actors deploy malicious “paymasters”—contracts ostensibly designed to sponsor gas fees for users.
When an unsuspecting user connects their wallet to what perfectly mimics a legitimate decentralized exchange, the malicious paymaster sneaks a hidden, fatal transaction into a batch. The user confidently signs a seemingly harmless off-chain message (EIP-712), genuinely believing they are simply verifying their identity. Instantly, their entire portfolio is violently drained via a batched transaction they never explicitly authorized.
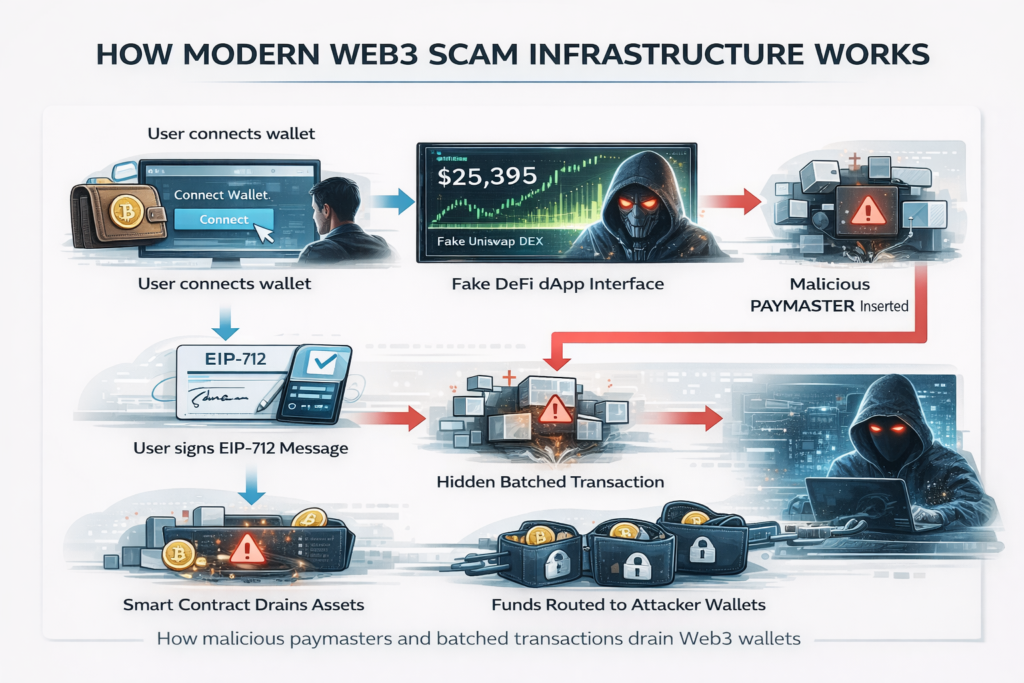
This terrifying level of obfuscation requires zero coding knowledge from the end-user, making it incredibly deadly. The scammers have fully industrialized this entire process. They actively sell “Scam-as-a-Service” kits deep on the dark web. For a minor upfront fee and a percentage of the stolen yield, literally anyone can deploy a highly polished, fully functional decentralized application (dApp) specifically engineered to siphon funds.
Furthermore, the seamless integration of Large Language Models (LLMs) into the deployment phase means these fake platforms feature absolutely flawless documentation. They generate whitepapers complete with advanced mathematical formulas, launch fake GitHub repositories with thousands of artificially generated commits, and spin up vibrant Discord communities populated entirely by AI agents conversing with each other to simulate organic hype.
Categorizing the Threat: Our Updated Cryptocurrency Scams List
To effectively defend your hard-earned portfolio, you must recognize the specific phenotypes of modern fraud. The days of simple, obvious rug pulls are fading rapidly. We are currently tracking a highly specific, constantly updated cryptocurrency scams list that highlights the most prevalent dangers currently plaguing the ecosystem.
Deepfake Multisig Compromise
Corporate treasury management within Web3 relies heavily on multi-signature (multisig) wallets. A standard transaction might require three out of five executives to explicitly sign off before any funds move. Scammers now entirely bypass the cryptographic security of the blockchain by hacking the human consensus mechanism instead.
Using just a few seconds of raw audio scraped from a crypto founder’s public Twitter Space, attackers perfectly train an AI voice clone. They then initiate a highly coordinated attack during vulnerable off-hours. The attacker calls a keyholder, sounding exactly like the CEO, frantically claiming an urgent server vulnerability requires immediate fund migration. They spoof the caller ID to add legitimacy. The panic is palpable. The false CEO aggressively demands an immediate multisig signature. The terrified victim, believing they are saving the protocol, signs the transaction. The treasury is emptied in seconds.

Cross-Chain Bridge Spoofing
Interoperability is often hailed as the holy grail of blockchain technology, but cross-chain bridges remain the desperately soft underbelly of Web3. In 2026, scammers are aggressively deploying shadow bridges. They flawlessly clone the frontend interfaces of popular protocols like Stargate or Across.
When a user attempts to bridge USDC from Ethereum to Arbitrum, the transaction appears completely normal. The user approves the token spend. However, the destination address parameter buried in the smart contract has been subtly hardcoded to route the funds directly to a mixer on an entirely different network, such as Monero or a privacy-centric zk-Rollup. Because the malicious transaction spans multiple distinct networks, tracing the stolen funds becomes an asymmetrical nightmare for on-chain forensic analysts.

Zero-Knowledge Airdrop Phishing
Airdrops remain a massive, incredibly popular driver of user acquisition. Scammers have successfully weaponized the complex cryptography behind Zero-Knowledge (ZK) proofs to execute devastating phishing campaigns. Users receive a legitimate-looking token in their wallet featuring a memo pointing directly to a claim dashboard. The dashboard loudly prompts the user to generate a “ZK proof of wallet ownership” to instantly claim a massive airdrop.
Instead of generating a harmless proof, the frontend interface covertly manipulates the user’s wallet software to sign a blanket, fatal approval for all ERC-20 tokens. The ZK element is purely theatrical—it is a smokescreen of complex terminology explicitly designed to make the user drop their guard. The exact moment the transaction is broadcast, a MEV (Miner Extractable Value) bot instantly front-runs any desperate attempt to revoke the approval, sweeping the wallet totally clean.
Real-World Targets: Notorious Fake Platforms Flagged in 2026
The abstract theories of theft become painfully real when we look at the specific platforms destroying retail wealth this year. According to major 2026 fraud watchdogs, the sheer volume of “phantom platforms” is staggering. Before interacting with any new exchange, cross-referencing platforms against a reputable hub like bitcoin scam watch is your only real line of defense.
Here are a few prominent examples of highly sophisticated, fake platforms currently devastating the market:
- BitcoinPrime.io: This platform leverages the allure of artificial intelligence, heavily marketing itself as an AI-powered automated bot capable of multiplying Bitcoin investments. In reality, it operates as an advanced fee fraud. It accepts initial deposits, then systematically blocks withdrawals, demanding endless “verification” or “network upgrade” fees until the user is entirely bled dry.
- AEL Exchange Wealth Management LTD: A devastating fake exchange that utilized heavily organized WhatsApp groups. They lured victims by promising “exclusive insider crypto trading signals.” After users deposited funds onto the beautifully designed (but entirely fake) trading interface, their balances were artificially inflated. When victims attempted to withdraw their massive “profits,” they were hit with exorbitant release fees before the platform ghosted them.
- CJB Crypto: This platform preyed on the desire for passive income through cloud mining. Promising guaranteed daily returns of 1.3%, they built an illusion of credibility by listing a fake UK residential address and stealing legitimate corporate registration details from an entirely unrelated business. It was a pure, unadulterated Ponzi scheme.
- https://www.google.com/search?q=Bit2meprojil.com (B2MP): Posing as a hyper-short-term investment hub, B2MP utilized human recruiters to build deep trust with potential victims. They fabricated complex “cooperation agreements” with legitimate US exchanges, convincing users to pool massive amounts of funds into a shadow contract that immediately drained their liquidity.
Post-Mortem: Analyzing the Biggest Cryptocurrency Scams of the Year
To truly grasp the absolute severity of the current situation, we must deeply analyze the mechanics of recent catastrophic failures. Examining the biggest cryptocurency scams of 2026 provides a brutal masterclass in modern exploitation techniques. Consider the devastating, sudden collapse of the “AuraLend” protocol.
AuraLend officially launched in Q1 2026. It was aggressively branded as a next-generation decentralized money market native to the Base network. It boasted well over $400 million in Total Value Locked (TVL) within its very first month. The code was heavily audited by two highly reputable security firms. The founders were supposedly fully doxed. It looked entirely bulletproof.
The reality was far darker. The exploit did not come from a traditional smart contract bug. It came from a highly sophisticated manipulation of the protocol’s decentralized oracle network. AuraLend relied heavily on a time-weighted average price (TWAP) oracle to determine the real-time value of collateral. The attackers astutely realized that due to a slight latency in the network’s block production times, the oracle’s price updates lagged behind real-time market data by roughly three fatal seconds.
The attackers flawlessly executed a massive flash loan—borrowing an astonishing $50 million in stablecoins with absolutely zero collateral, provided the loan was repaid perfectly within the exact same block. They weaponized this massive capital injection to aggressively dump an illiquid governance token associated with AuraLend across multiple decentralized exchanges. This artificially crashed the token’s market price to zero.
Because of that tiny three-second oracle lag, AuraLend’s smart contracts still blindly believed the governance token was worth its original, highly inflated price. The attackers swiftly deposited the now-worthless tokens directly into AuraLend as collateral and borrowed millions of dollars in actual, hard stablecoins (USDC and DAI) against it. They then successfully repaid the initial flash loan. All of this incredible financial destruction occurred within a single block.
Approximately 12 seconds later, the oracle finally updated, fully recognizing the collateral was utterly worthless. But the attackers had already successfully absconded with $112 million in clean stablecoins.
The funds were immediately pushed through an automated, decentralized mixer via thousands of micro-transactions, making recovery virtually impossible. The highly publicized “doxed” founders? They were incredibly convincing deepfake personas generated by a sophisticated cyber syndicate operating out of Eastern Europe. The bustling GitHub activity was entirely scripted. The audits were real, but the auditors fundamentally missed the subtle economic vulnerability regarding oracle latency because they were exclusively looking for traditional code errors like reentrancy attacks.
Technical Nuances: How AI Changes the Phishing Game
While the catastrophic AuraLend disaster vividly highlights how complex economic exploits operate, the daily threat to average retail users is entirely psychological. The automation of spear-phishing represents a massive paradigm shift.
Historically, phishing attacks were merely a numbers game. Attackers blindly sent a million emails simply hoping ten gullible people would click a malicious link. In 2026, AI effortlessly allows attackers to execute highly targeted, hyper-personalized spear-phishing campaigns at a massive scale. An LLM agent silently monitors the blockchain for large, dormant wallets that suddenly become active. When a target wallet finally executes a transaction, the AI scours social media, Discord, and Telegram to immediately cross-reference the wallet address with a specific user identity.
Once definitively identified, the AI instantly crafts a bespoke attack narrative. If the user recently interacted with a specific NFT marketplace, the AI dynamically generates an email that looks exactly like a high-priority support ticket from that specific marketplace, accurately referencing the exact transaction hash, time, and gas fee of the user’s very last trade. The email urgently warns of a failed smart contract execution and provides a helpful link to “salvage” the funds. The level of contextual accuracy is absolutely terrifying. It completely bypasses the natural skepticism of even veteran crypto traders.
Furthermore, these AI systems dynamically adapt on the fly. If a cautious user replies to a phishing email with suspicion, the LLM responds in real-time, perfectly matching the tone and technical jargon of a senior blockchain developer. It calmly addresses the user’s specific concerns, actively provides fake Etherscan links to mathematically “prove” its legitimacy, and slowly, methodically manipulates the victim into authorizing a malicious transaction. The human element has been entirely removed from the scammer’s side, allowing them to ruthlessly target thousands of high-net-worth individuals simultaneously with bespoke, highly convincing narratives.
Defensive Protocols for Web3 Users
Pure survival in this deeply hostile environment requires a fundamental shift in your operational security. Relying on outdated antivirus software or basic hardware wallets is absolutely no longer sufficient. You must aggressively adopt an institutional-grade security mindset.
First, you must implement strict wallet compartmentalization. Never, under any circumstances, interact with unverified smart contracts using a wallet that holds significant assets. Maintain a highly guarded “cold” vault that physically never signs any transactions other than plain token transfers directly to your own secondary addresses. Use a separate “warm” wallet exclusively for holding mid-tier assets, and a completely isolated “hot” burner wallet for interacting with new dApps, claiming airdrops, or minting NFTs. Only ever fund the burner wallet with the exact amount of capital required for the immediate transaction. If the burner wallet is compromised, the damage is heavily localized and negligible.
Second, aggressively utilize advanced transaction simulation tools. Before signing any transaction, route it through a local simulation extension. These incredibly powerful tools fork the blockchain state locally and execute the pending transaction safely in a sandbox, explicitly showing you exactly what assets will leave your wallet and what will enter. If a decentralized exchange transaction shows that your entire balance of Lido Staked ETH will be silently drained alongside the token you are trying to swap, the simulation will unequivocally catch it before the blockchain irrevocably executes it.
Third, become utterly militant about revoking token approvals. When you successfully interact with a decentralized exchange, you usually grant the smart contract an infinite approval to spend a specific token. This theoretically saves gas on future trades. However, if that exchange’s smart contract is ever upgraded maliciously or hacked, the attacker can effortlessly drain your wallet months later. Make it a strict weekly habit to strip permissions from any contract you are not actively, currently using.
The Future of On-Chain Forensics and Regulatory Response
The terrifying escalation of these threats has triggered a massive, coordinated response from global regulatory bodies and elite blockchain analytic firms. The forensic tools of 2026 are highly advanced, routinely utilizing cutting-edge machine learning algorithms to map incredibly complex transaction graphs across dozens of layer-2 networks simultaneously.
Authorities are increasingly treating smart contract deployments as verifiable, binding legal actions. The updated Markets in Crypto-Assets (MiCA) framework in Europe and the latest SEC guidelines in the United States now mandate strict liability for protocol developers who carelessly launch platforms with gross economic vulnerabilities or deeply hidden backdoors. We are actively seeing a massive rise in “on-chain subpoenas,” where law enforcement agencies send encrypted messages directly to the public wallet addresses of suspected hackers, heavily embedded with digital tracking beacons.
Furthermore, powerful decentralized security networks are finally emerging. These innovative protocols crowdsource critical threat intelligence, allowing elite white-hat hackers to actually stake capital against the verified security of specific smart contracts. If a malicious contract is definitively identified, the network automatically blacklists the associated addresses across thousands of participating frontends, effectively quarantining the scammer’s stolen assets well before they can bridge them to an untraceable privacy network.
The brutal arms race between decentralized fraud and robust on-chain security will never truly end. As brilliant developers relentlessly build more complex financial primitives, attackers will inevitably find more obscure ways to break them. The ultimate responsibility strictly rests with the individual user. Deep education, extreme skepticism, and rigorous operational security are your only true defenses. The platforms may change, the underlying technology may heavily evolve, but the fundamental, golden rule of Web3 remains absolute: verify everything, trust nothing.
To ensure you stay one step ahead of these evolving threats, always verify a platform’s legitimacy before connecting your wallet. Explore real-time threat intelligence, report suspicious activity, and consult the most accurate, frequently updated database of malicious actors directly at Bitcoin Scam Watch.