The greatest lie ever sold to the modern digital investor is the myth of absolute cryptocurrency anonymity. For years, cybercriminals, rogue developers, and international syndicates operated under the false assumption that moving digital wealth across the blockchain was equivalent to handing over unmarked cash in a dark alley.
They were wrong.
While the user interface of Web3 might feel opaque, the underlying architecture is the most transparent, aggressively unblinking financial surveillance system ever created. Every single transfer, every swapped token, and every fraction of a cent moved across networks like Ethereum and Tron is permanently etched into a public ledger. It cannot be deleted, altered, or followed.
In 2026, stablecoins like Tether (USDT) have become the undisputed primary targets for sophisticated threat actors running devastating Pig Butchering operations, massive DeFi Exit Scams, and automated Rug Pulls. Scammers love USDT because it perfectly mirrors the US Dollar, insulating their illicit gains from the infamous volatility of the broader crypto market.
However, the exact same cryptographic technology that allows these criminals to siphon funds across the globe in seconds also leaves a permanent, undeniable public paper trail. The era of the “untraceable hack” is rapidly closing. Today, successfully deciding to recover stolen cryptocurrency 2026 style relies entirely on the deployment of elite blockchain forensics.
This comprehensive guide serves as your technical breakdown. We will explore exactly how modern investigators leverage blockchain analysis to trace, attribute, and legally recover stolen USDT.
The Evolution of the Crime: Why USDT is the Cartel Currency of Choice
Before we can hunt the adversary, we must understand their mechanics. Why do modern scammers overwhelmingly prefer USDT over Bitcoin or Ethereum?
The answer lies in simple, cold economics. Criminal syndicates operating out of Southeast Asia or Eastern Europe are running massive businesses. They have payrolls, server costs, and real-world expenses. If a syndicate steals $1 million in Bitcoin, and the market crashes 20% the next day, they have lost $200,000 to market dynamics. USDT, pegged 1:1 with the US Dollar, provides a safe haven. It is the perfect digital fiat.
Furthermore, USDT operates fluidly across multiple blockchains. While ERC-20 (the Ethereum network version of USDT) is incredibly popular, the TRC-20 (Tron network) variant is arguably the gold standard for illicit transfers. Why? Because Tron network fees are fractions of a penny, and transaction speeds are nearly instantaneous.
This speed facilitates the three most devastating fraud models of 2026:
- Pig Butchering Scams: Highly tailored, months-long psychological operations where victims are slowly convinced to transfer their life savings into fake trading terminals.
- DeFi Exit Scams: Malicious protocol developers build legitimate-looking decentralized finance platforms, accumulate hundreds of millions in user liquidity (Total Value Locked), and then trigger hidden “backdoors” in the smart contract code to drain all deposited USDT simultaneously.
- Advanced Spear Phishing: Utilizing AI-generated emails and deepfake videos to trick users into signing malicious zero-knowledge proofs that instantly drain their hot wallets.
When the screen goes dark and your balance reads zero, the clock starts ticking. The criminals are moving fast. But blockchain forensics moves faster.
Demystifying Blockchain Forensics: What Is It Exactly?
At its core, blockchain analysis is the highly specialized process of examining, interpreting, mapping, and visualizing raw hexadecimal data pulled directly from a blockchain network. The primary objective is to understand complex transaction patterns, identify the real-world entities controlling anonymous wallet addresses, and physically trace the flow of stolen funds.
Think of it as digital DNA sequencing for money.
Because USDT operates on public ledgers, privacy is an illusion. A wallet address (a long string of alphanumeric characters) might not have a name attached to it natively, but its behavior screams its identity. Blockchain forensics experts do not merely look at Etherscan or Tronscan and follow a single line. They ingest massive datasets into proprietary graph databases.
They utilize advanced probabilistic heuristics—complex algorithms that analyze transaction timing, gas fee spending patterns, and network node IP leaks. By analyzing how a specific wallet interacts with other wallets, forensic scientists can cluster thousands of seemingly random, anonymous addresses together, proving beyond a shadow of a legal doubt that they are all controlled by the exact same criminal entity.
Step-by-Step: How Investigators Trace Stolen USDT
The process of tracing stolen USDT is an exhausting, highly technical game of digital cat and mouse. Criminals employ automated scripts designed to obfuscate the money trail, but these scripts leave distinct, recognizable behavioral signatures.
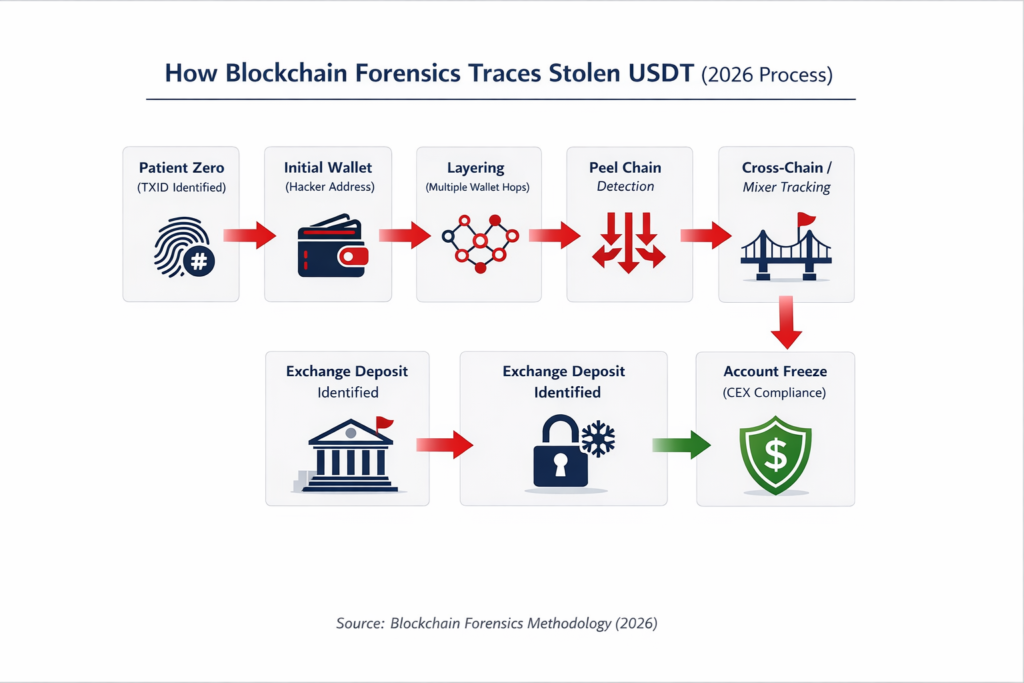
Here is the exact blueprint investigators use to trace stolen USDT in 2026.
Phase 1: Identifying the “Patient Zero” Transaction
Every forensic investigation must begin at the scene of the crime: the victim’s wallet. The absolute first step is locating the exact Transaction ID (TXID) or “hash” where the USDT was initially, illicitly transferred out of the victim’s control.
This TXID is the digital fingerprint of the theft. It serves as “Patient Zero.” By isolating this specific starting point, investigators establish the absolute baseline of the money trail. From this single hash, analysts can extract the timestamp, the exact amount stolen down to the decimal, the network used (ERC-20, TRC-20, BEP-20, etc.), and the first malicious receiving address.
Phase 2: Mapping the “Hops” and Layering Techniques
Scammers are rarely stupid enough to keep stolen USDT sitting in one place. If they leave the funds in the initial receiving wallet, they are a sitting duck for a freeze order. Therefore, they utilize a classic money laundering technique adapted for Web3 known as “layering.”
Layering involves moving the stolen funds rapidly through dozens, sometimes hundreds, of intermediary wallets. In the industry, these are referred to as “hops.” A syndicate might steal $500,000 in USDT, immediately split it into fifty separate transactions of $10,000, and send those fractions to fifty different wallets. Five minutes later, those fifty wallets send the funds to two hundred new wallets.
To the untrained eye looking at a standard block explorer, the money has vanished into a chaotic web of meaningless numbers.
However, elite blockchain forensics experts deploy advanced visualization tools. These software suites automatically trace every single hop, piercing through the noise. The software maps the flow of tokens visually, creating a massive spiderweb graph on the investigator’s screen. No matter how many times the scammer splits, moves, or transfers the USDT, the total volume remains mathematically constant. The software simply follows the math.
Phase 3: Unraveling the “Peel Chain”
As the investigation dives deeper into the blockchain, analysts aggressively watch for specific laundering behaviors. The most prominent tactic used to wash massive amounts of illicit USDT is the notorious “peel chain.”
Imagine an onion. You have a massive core, and you slowly peel off tiny, paper-thin layers one by one. This is exactly how a peel chain operates.
A scammer controlling a wallet holding $2 million in stolen USDT needs to liquidate those funds. However, if they suddenly deposit $2 million into a regulated exchange like Coinbase or Binance, the exchange’s automated Anti-Money Laundering (AML) algorithms will instantly flag the transaction, freeze the account, and alert authorities.
To bypass this, the scammer initiates a peel chain. The main wallet transfers $1,995,000 to a brand new, seemingly clean wallet. Simultaneously, it “peels” off $5,000 and sends it to an exchange deposit address.
The new wallet holding the $1,995,000 then repeats the process. It sends $1,990,000 to another new wallet, and peels off another $5,000 to a different exchange account. This automated process loops hundreds of times. The scammer bleeds the massive bankroll dry through thousands of tiny, seemingly innocuous micro-deposits, hoping to slip under the radar of the exchange’s compliance threshold.
Blockchain analysis utterly destroys this tactic. Heuristic algorithms easily recognize the distinct structural pattern of a peel chain. The forensic software automatically tags the entire chain of hundreds of wallets as a single, contiguous criminal operation, rendering the scammer’s obfuscation useless.
Phase 4: Navigating Decentralized Mixers and Cross-Chain Bridges
In 2026, standard layering and peel chains are often not enough for elite syndicates. They frequently attempt to break the forensic link entirely by utilizing decentralized mixers or cross-chain bridges.
A mixer is a smart contract that pools together USDT from hundreds of different users, jumbles the tokens together, and then allows users to withdraw clean tokens from a different address. The goal is to break the deterministic link between the deposit and the withdrawal.
Similarly, cross-chain bridges allow a scammer to swap their TRC-20 USDT on the Tron network for an equivalent asset on the Solana network, and then bridge it again to the Avalanche network. They are attempting to jump across entirely different blockchains to lose the investigator.
This is where true blockchain forensics shines. Advanced investigators utilize “cross-chain analytics.” By monitoring the liquidity pools of these bridges, analysts track the precise timing and volume of the swaps. If a hacker deposits exactly 45,392 USDT into an Ethereum bridge, and exactly 14 seconds later, a brand new wallet on the Polygon network receives 45,389 USDC (accounting for the automated slippage fee), the investigator mathematically links the two wallets across different networks.
The blockchain never lies. The math always balances.
Phase 5: The Ultimate Goal – Identifying the Cash-Out Point
The entire purpose of blockchain forensics boils down to one critical objective: identifying the final destination of the stolen funds.
Scammers do not hack wallets just to look at digital numbers on a screen. They steal crypto to buy real-world assets—mansions in Dubai, luxury sports cars, or massive server farms. To accomplish this, they face a massive, unavoidable bottleneck. They cannot buy a house with stolen USDT sitting in a decentralized MetaMask wallet. They must eventually convert that digital token into cold, hard fiat currency (USD, EUR, GBP).
To convert crypto to fiat, they are forced to use an off-ramp. Almost universally, this means depositing the stolen USDT into a Centralized Cryptocurrency Exchange (CEX) or an Over-The-Counter (OTC) trading desk.
This is their fatal flaw. This is the moment the trap snaps shut.
Recover Stolen Cryptocurrency 2026: The Legal and Technical Recovery Protocol
Tracing the funds is only the first half of the battle. Once the stolen USDT is successfully traced to a deposit address belonging to a centralized exchange—such as Binance, Kraken, OKX, or Crypto.com—the active recovery phase aggressively begins.
This is the intersection where complex mathematics meets international law. Here is how you successfully recover stolen cryptocurrency 2026.
1. The KYC Vulnerability
Unlike decentralized wallets, centralized exchanges operate strictly within the bounds of traditional financial regulation. They heavily comply with global Know Your Customer (KYC) and Anti-Money Laundering (AML) laws.
When the scammer opened the account at that exchange to cash out your USDT, they were legally forced to hand over their real-world identity. They submitted a government-issued passport, a driver’s license, proof of residential address, and subjected themselves to live facial recognition scans.
2. The Forensic Report and The Preservation Letter
You cannot simply email an exchange, claim your funds were stolen, and ask for them back. Exchanges require absolute, undeniable proof.
This is why a professional, institutionally recognized blockchain analysis report is mandatory. A certified forensic investigator compiles the entire mapped trace—detailing every hop, exposing the peel chains, and definitively proving the lineage of the funds from your “Patient Zero” transaction directly to the scammer’s exchange deposit address.
Simultaneously, specialized Web3 attorneys draft a “Letter of Preservation.” This legal document is blasted to the exchange’s legal department, putting them on official notice that stolen assets are currently sitting on their platform. This legally compels the exchange to instantly freeze the scammer’s account, preventing them from withdrawing the fiat currency.
3. Subpoenas and The “John Doe” Lawsuit
With the assets effectively frozen in escrow by the exchange, the final legal maneuver begins. Because the victim still does not know the true name of the hacker, their legal team files a civil “John Doe” lawsuit against the anonymous owner of the deposit address.
This brilliant legal strategy grants the presiding judge the authority to issue a binding, international subpoena directly to the centralized exchange. The subpoena legally forces the exchange to crack open their highly secured vault and hand over the scammer’s complete KYC profile to law enforcement and the victim’s legal counsel.
Suddenly, the ghost in the machine has a name, a home address, and a face. From this point, the recovery transitions from a complex cryptographic puzzle into a standard, traditional asset seizure and forfeiture process.
The Devastating Threat of Recovery Room Scams
We must address a critical, devastating reality of the 2026 crypto landscape. When victims realize their USDT has been stolen, they panic. They frantically search Google and social media for help.
This desperation makes them prime targets for “Recovery Room Scams.”
The internet is absolutely flooded with fake “white-hat hackers,” fraudulent cybersecurity firms, and malicious actors claiming they can “hack the blockchain” or deploy a “reverse smart contract” to magically pull your stolen funds back into your wallet for a small upfront fee.
Listen closely: It is technologically impossible to reverse a blockchain transaction.
No one can hack the Bitcoin or Ethereum network to get your money back. Anyone promising guaranteed, immediate retrieval via software hacking is a scammer trying to victimize you a second time.
Legitimate asset recovery is a meticulous, highly regulated process that heavily relies on immutable blockchain forensics, close cooperation with international law enforcement, and aggressive legal subpoenas served to centralized exchanges. It takes time, expertise, and institutional credibility.
Reclaiming Your Digital Sovereignty with Bitcoin Scam Watch
The psychological toll of losing your digital assets to a massive DeFi Exit Scam or a targeted spear-phishing attack is immense. The syndicates operating these frauds rely entirely on your feelings of hopelessness. They want you to believe the money is gone forever, swallowed by the anonymous void of the blockchain.
Do not give them that satisfaction. The blockchain is an unblinking eye. The money left a trail, and that trail can absolutely be followed.
If your USDT has been stolen, every single second counts. The faster you act, the higher the probability of intercepting the funds before they successfully clear the complex laundering cycle and off-ramp into untraceable fiat currency. You need institutional-grade tracking, certified forensic reports, and expert guidance to navigate the legal complexities of freezing centralized exchange assets.
Do not navigate this nightmare alone, and do not fall victim to secondary recovery scams. For immediate, professional triage, vetted forensic intelligence, and a clear roadmap to reclaiming your digital wealth, engage the experts immediately at Bitcoin Scam Watch. Trust the math, follow the ledger, and strike back.
