The exact moment you realize your digital wallet has been completely drained is a visceral, deeply unsettling experience. One minute, your portfolio brilliantly reflects years of patient investing, disciplined trading, and decentralized finance (DeFi) participation. The next second? A cold string of unauthorized transactions leaves behind nothing but a zero balance.
Panic instantly sets in. We are taught that the blockchain is famously immutable. Transactions cannot be reversed. But here is the critical truth that syndicates don’t want you to know: immutable absolutely does not mean invisible.
The landscape of crypto theft has mutated rapidly. We are operating far beyond the nostalgic days of simple typosquatting or rudimentary phishing links. Today’s criminal syndicates operate exactly like sophisticated, multinational tech corporations. They deploy quantum-resistant wallet drains, weaponize artificial intelligence deepfakes capable of perfectly mimicking exchange support staff, and execute highly complex zero-day exploits directly targeting smart contract logic. Yet, the forensic tools built to track and reclaim these stolen assets have evolved at an equally aggressive, terrifying pace.
Reclaiming your lost assets is no longer a pipe dream reserved strictly for institutional whales or heavily armed government agencies. Through aggressive on-chain forensics, targeted cross-border legal maneuvers, and the ruthless intervention of specialized investigators, retail victims are finally fighting back.
This comprehensive guide breaks down the exact mechanisms, aggressive legal strategies, and technical realities required for the successful Recovery Stolen Cryptocurrency process in 2026.
The State of Crypto Theft in 2026: Anatomy of an Exploit
To successfully defeat an adversary, you must first deeply understand their methodology. The romanticized days of a lone hacker guessing seed phrases in a dark basement are over. The contemporary threat landscape is entirely dominated by highly organized, massively funded syndicates.
Here is what is actively draining wallets right now:
- AI-Driven Spear Phishing: Attackers aggressively utilize large language models to scrape a target’s social media, professional LinkedIn history, and public blockchain interactions. They then generate hyper-personalized, lethal communications. You might receive a synthetic voice call from someone sounding exactly like your trusted OTC broker, calmly guiding you to “secure” your assets by signing a new smart contract. Once signed, that malicious contract grants the attacker infinite approval to drain your ERC-20 tokens instantly.
- Cross-Chain Bridge Exploits: Hackers specifically target the massive liquidity pools connecting distinct blockchains, such as the bridges between Ethereum and Solana. By identifying obscure logic errors in the governing smart contracts, they siphon millions in wrapped assets. They then immediately trigger a process known as “chain hopping”—violently moving the funds across dozens of different blockchains and decentralized exchanges (DEXs) to shatter the forensic trail.
- Industrial Pig Butchering: These long-term, psychologically devastating confidence tricks involve building a completely fake romantic or platonic relationship with the victim over several months. Eventually, the trusting victim is coaxed into investing capital into a fraudulent trading platform that looks entirely, flawlessly legitimate. The numbers on the screen go up, but the actual funds are funneled directly into the scammer’s offshore wallets.
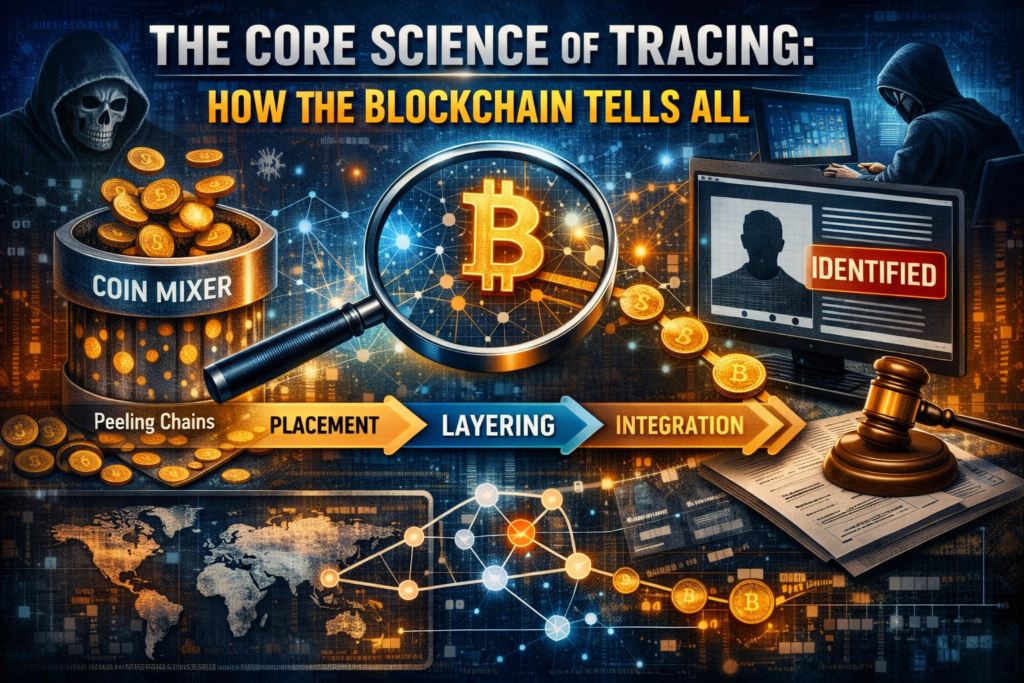
The Core Science of Tracing: How the Blockchain Tells All
Despite the incredibly sophisticated obfuscation tactics employed by modern thieves, the foundational architecture of blockchain technology remains a transparent, public ledger. Every single token movement, every decentralized swap, and every fractional gas fee paid leaves a permanent cryptographic fingerprint. This is exactly where advanced on-chain analytics enter the battlefield.
When a massive theft occurs, the funds rarely sit idle. The attacker must launder the crypto to eventually convert it into usable fiat currency. This complex process involves three distinct stages:
- Placement: The stolen funds are moved from the victim’s wallet to a temporary staging address.
- Layering: The complexity aggressively scales up. Attackers push the funds through decentralized coin mixers, split the assets into hundreds of smaller, erratic transactions (a technique known as “peeling chains”), and utilize obscure privacy protocols.
- Integration: The washed funds hit a centralized exchange to be sold for fiat.
However, elite forensic tools in 2026 possess unprecedented, terrifying capabilities. Blockchain intelligence software utilizes powerful “heuristic clustering.” This algorithmic approach rapidly analyzes transaction patterns to group multiple, seemingly unrelated digital addresses under one single real-world entity. If an attacker uses a fresh address to receive stolen Bitcoin, but later accidentally pays a tiny mining fee from an older address previously linked to a known darknet market, the software instantly connects the dots. The scammer’s pseudo-anonymity is violently shattered.
Even privacy-centric obfuscation tools are no longer bulletproof. By meticulously analyzing the precise timing of deposits and withdrawals, the exact fractional amounts, and the specific gas prices paid, elite forensic analysts can often “demix” the transactions with a shockingly high degree of mathematical probability.
Immediate Triage: Surviving the Golden Hours
Time is your absolute most valuable commodity in the direct aftermath of a security breach. The specific actions taken in the first 24 to 48 hours heavily dictate the ultimate success or failure of the retrieval effort. If you discover a compromise, execute this triage protocol without hesitation.
1. Isolate and Disconnect
If you suspect your physical device is compromised, immediately disconnect it from the internet. Do not simply close the browser tab; physically sever the Wi-Fi or violently unplug the ethernet cable. If the breach involves a hot wallet (like MetaMask), do not attempt to send more funds to that wallet to pay for gas fees to rescue remaining assets. The attacker likely has an automated “sweeper bot” installed. The millisecond native tokens arrive for gas, the bot transfers everything out before you can click send.
2. Revoke Smart Contract Approvals
If the theft resulted from a malicious digital signature, your wallet might remarkably still hold some assets, but the attacker currently retains permission to take them later. Immediately use block explorer tools (like Etherscan’s Token Approval tool) or dedicated revocation services to cancel all active allowances. This acts as a vital digital tourniquet, immediately stopping further bleeding.
3. Preserve the Cryptographic Evidence
Do not delete apps, do not clear your browser history, and absolutely do not wipe your computer. You desperately need the forensic trail intact. Document everything. Create a master spreadsheet recording the exact date and time of the unauthorized transactions, the transaction hashes (TxID), the sender and receiver addresses, and the specific networks involved.
4. Alert the Centralized Exchanges (CEXs)
The ultimate goal of almost every thief is to cash out into fiat. To do this, they almost always have to move the funds to a centralized exchange that strictly enforces Know Your Customer (KYC) regulations. If you can track the funds to a Binance, Kraken, or Coinbase deposit address, instantly contact their security teams. While exchanges will not return funds based solely on an angry email, they frequently freeze the suspect accounts pending a formal law enforcement request.
Hiring a Funds Recovery Expert: Vetting the Professionals
The sheer complexity of modern blockchain forensics means that DIY tracing is rarely, if ever, sufficient for a successful legal recovery. You will need to retain a specialized professional. A legitimate investigator operates seamlessly at the intersection of high-level cybersecurity, data science, and international law.
These professionals do not use magic or “hacking.” They use enterprise-grade software that costs tens of thousands of dollars annually. They meticulously map the flow of funds, generating comprehensive, legally admissible affidavit reports. A judge will not issue a subpoena or a freeze order based on a victim’s personal spreadsheet; they strictly require a sworn statement from a certified forensic investigator detailing the exact cryptographic path the stolen assets took.
When seeking representation, look for investigators holding recognized industry certifications, such as the Chainalysis Reactor Certification (CRC). A true professional will set grounded, realistic expectations. If the funds have been permanently bridged to a highly obscure, illiquid privacy chain with zero centralized touchpoints, a reputable expert will flatly tell you the chances of recovery are exceedingly low, saving you from throwing good money after bad.
Navigating the Legal Labyrinth: Subpoenas and Freeze Orders
Tracing the assets directly to a specific exchange is only half the battle. The second half is a high-stakes, aggressive legal procedural.
Because the blockchain is pseudo-anonymous, your forensic report points to a deposit address, not a name. You know where the money is, but you do not know who actively controls the account. In jurisdictions like the United States or the United Kingdom, specialized attorneys will file a “John Doe” lawsuit against an unknown defendant. Once filed, the judge officially grants the victim’s legal team subpoena power. The attorney aggressively serves a subpoena duces tecum on the centralized exchange where the funds currently reside.
This subpoena legally compels the exchange to turn over the KYC data associated with the suspect account. This data dump typically includes the account holder’s legal name, government-issued ID, physical address, and linked bank accounts. Suddenly, the anonymous hacker is completely unmasked.
Simultaneously, the attorney will file for an emergency ex parte injunction—a freeze order. This legally prevents the exchange from allowing the suspect to withdraw or trade the frozen assets before they even realize they are being targeted.
The Epidemic of Secondary Scams: Defending Yourself Twice
Perhaps the most tragic, infuriating aspect of losing digital assets is the vultures that begin circling immediately afterward. The internet is flooded with predatory operations promising guaranteed, frictionless recovery. These are secondary scams, designed specifically to brutally exploit victims who are already in a state of extreme emotional and financial distress.
You must understand one immutable, absolute fact: Nobody can “hack back” the blockchain. It is cryptographically impossible to force a reverse transaction on a decentralized network like Bitcoin or Ethereum without controlling 51% of the network’s global hash rate. Anyone claiming they can simply inject malicious code to retrieve your tokens is blatantly lying to you.
Red flags of a secondary recovery scam include:
- Guarantees of Success: Legitimate investigators never, ever guarantee a successful recovery. The variables are far too immense.
- Demands for Upfront Crypto Payments: Reputable forensic firms generally accept traditional fiat payments via wire transfer, offering legal recourse and clear paper trails.
- Requests for Private Keys: A legitimate investigator will absolutely never need your seed phrase or private keys to trace public funds. If they ask for your keys, they are actively trying to steal whatever you have left.
Preventative Measures: Making Your Portfolio Untouchable
Recovery is arduous, highly expensive, and emotionally draining. The ultimate, absolute strategy is rendering your assets totally untouchable in the first place.
- Smart Contract Wallets: The transition away from traditional accounts relying on a single seed phrase is rapidly accelerating. Smart contract wallets utilizing account abstraction offer highly programmable security, allowing you to implement strict daily withdrawal limits.
- Multi-Party Computation (MPC): MPC technology entirely removes the single point of failure. The private key is never generated in whole. Instead, cryptographic shards are distributed across multiple devices. Even if a hacker fully compromises your primary device, they only obtain a completely useless fragment of the puzzle.
- Rigorous Auditing: Before interacting with any decentralized application, verify its security posture. Use advanced browser extensions that simulate transactions safely in a sandbox before you sign them, showing you in plain English exactly what assets will move.
The trauma of having your digital wealth stripped away is profound. The blockchain is cold, mathematical, and deeply unforgiving, but it is also the ultimate, unblinking witness. By deploying the strategies outlined in this guide, assembling a team of verified experts, and acting with absolute precision, you transform from a helpless victim into an active, dangerous participant in the pursuit of justice.
For continuous threat intelligence, vetted recovery guidance, and the truth about the Recovery Stolen Cryptocurrency process, ground your research at trusted hubs like Bitcoin Scam Watch. The fight for your assets is entirely within your control.
